HoneyDocker Real-time Analysis and Management Framework
Department of Computer Science and Engineering
Project Abstract
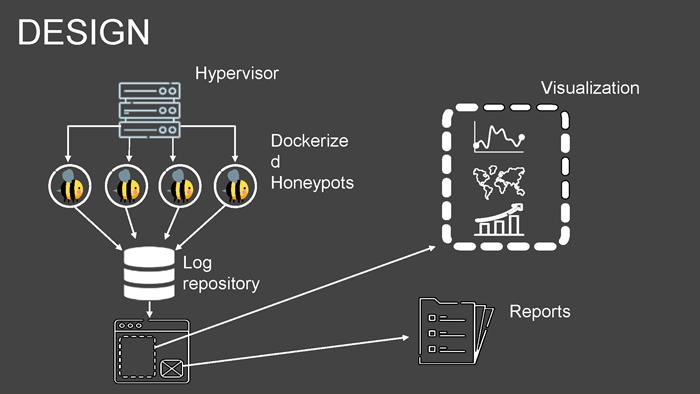
In this day and age, cyber attacks are very prevalent. For the people working on the defense side of cyber security, it is a game of knowing your enemy. With this in mind, we’ve built a standalone system for controlling honeypots, which capture cyber attacks and relay that information to the network admin.
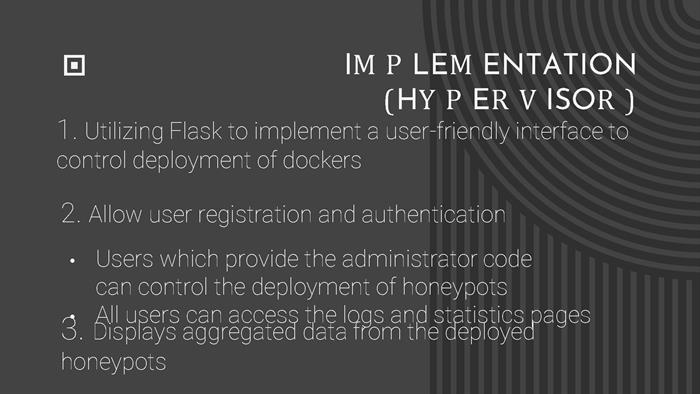
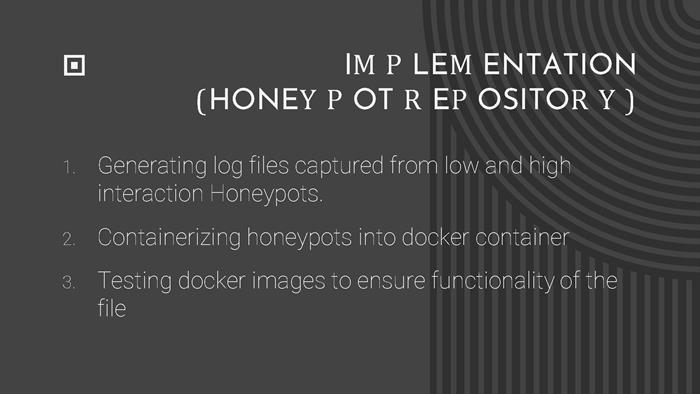
Our project is a static management system for running and analyzing honeypots. We’ve created a full web application using Bootstrap, Flask, MongoDB, Docker (and SDK for python), which allows admins of a network to deploy and analyze a variety of honeypots. We implemented the honeypots in Docker because it is lightweight, efficient, and it prevents applications from interfering with each other. The system includes 3 honeypots: one low interaction SSH, one high interaction HTTP (with mysql, tomcat server, java servlets) and one low interaction SMB. Each of these honeypots provides attack logging and data aggregation.
The web portal has access control implemented, with salting and hashing used in our database for user passwords. Admins have permission to access a page that allows them to start and stop honeypot docker containers and view the logs for each container. With this system, we hope to help network admins have a better understanding of the attack patterns happening outside their network.